Windows forensic artefacts are one of the core evidence sources used in DFIR investigations, but investigations often fail not because analysts cannot extract artefacts, but because they over-interpret them. This article explains how to treat Windows artefacts as evidence, not indicators, and how to reason about them defensibly.
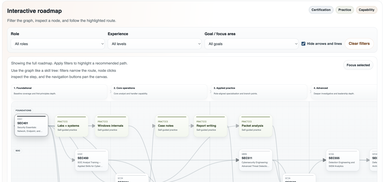
I'm in no way saying that certs or degrees are the only path to success. There are definitely individuals in the field who've never taken a cert or completed a degree and are super successful. However, I think those individuals are rare, they're the exception (i.e. exceptional). In my experience (and it's only my experience I can speak from), certs are the fastest way to get skilled up in an area where you have knowledge gaps. With that said, let's get started.
It can be difficult when there are so many different roles and job titles and little standardisation. The requirements for a role can differ vastly depending on the hiring manager and the HR team (not to call anyone out, it's a fast moving field and it's hard to keep up). There's no shortage of advice like this; I realise of course that a quick Google search brings up a multitude of similar blogs, but if people are still asking 'where do I start,' at least having written this I have somewhere to point them for a quick rundown of my thoughts.
If you've been following this series, you've already done the hardest part. You've stopped treating Windows artefacts as indicators that mean something, and started treating them as evidence that supports a specific claim under specific conditions.
This series is deliberately slow. It's trying to build an instinct, not a checklist.
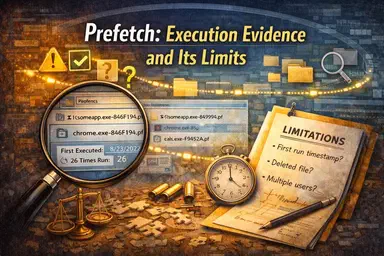
In the first article, we framed Windows artefacts as partial, contextual evidence rather than deterministic indicators. In the ShellBags post, we applied that framing to a common mistake: treating shell navigation as proof of file access or intent. ShellBags are a record of what File Explorer remembers about where a user navigated and how those folders were rendered. That's valuable. It's also easy to over-interpret.
What actually changes when moving from SOC analyst to incident responder? A practical breakdown of skills, mindset, and decision-making in real-world DFIR roles.
ShellBags are one of the most useful Windows navigation artefacts in DFIR, but also one of the easiest to over-interpret. This article explains what ShellBags actually record, what they can support as evidence, and why navigation is not the same as file access, execution, or intent.
The Windows Recycle Bin is one of the most useful deletion artefacts in DFIR, but also one of the easiest to over-interpret. This article explains how $I and $R files work on Windows 10 and 11, what Recycle Bin evidence can reliably support, and how to use it defensibly in incident response investigations.
Here's a quick write‑up on Alternate Data Streams (ADS). An ADS is a file attribute used in NTFS that can provide investigators with valuable evidence that might otherwise be overlooked.
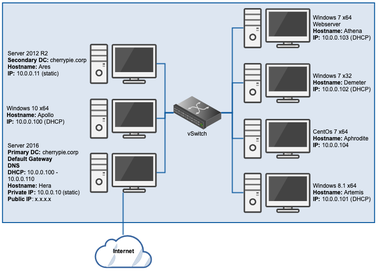
This (for now anyway) will be the last post in this series, in which we'll add a CentOS 7 x64 workstation to our lab.